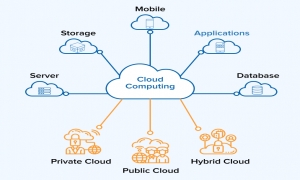
Organizations know the value of the cloud very well, and most of them migrate their operations to the cloud as soon as possible. Especially considering the pandemic and the increasingly natural nature of remote work. However, there are major challenges associated with moving to the cloud. This includes the diversity and breadth of the network and the security controls and reliance on legacy systems are difficult to overcome. Previous security mechanisms, such as classic perimeter protection using firewalls, need to be rethought. Current customers want to deploy private and/or public clouds, but still need to maintain certain on-premises elements and ensure that connectivity and security are properly maintained in this hybrid structure.
But how high is the security cost when you look at the entire hybrid network? Six best practices for security management in hybrid clouds are outlined here:
1. Use next generation firewall
Nearly half (49 percent) of companies stated that they operate a virtual edition of a conventional firewall in the cloud. It is becoming increasingly clear that the cloud provider's native security controls are insufficient and a next-generation firewall solution is needed. While conventional stateful firewalls are designed to monitor incoming and outgoing network traffic, next-generation firewalls (NGFW) include functions such as application awareness and control, integrated breach prevention, and active threat intelligence. In other words, while conventional firewalls allow level 1 to 2 protection, NGFW offers level 3 to 7 protection.
2. Use dynamic objects
On-premises security is usually easier because subnets and IP addresses are mostly static. However, in the cloud, workloads are dynamically assigned and serviced, IP addresses change, so conventional firewalls can't keep up. NGFW dynamic objects allow organizations to map a group of workloads by cloud-native category and then use those objects in policies to properly enforce traffic and avoid the need to update policies frequently.
3. Complete visibility
As with any form of security, visibility is critical. Without this, even the best preventive or corrective strategies will fail. Security must be continuously evaluated in all work processes, both related to the cloud services used and Internet clients and data centers . A single overview of the entire network is invaluable when it comes to hybrid cloud security.
4. Assess overall risk
Too many companies are guilty of focusing solely on cloud services when managing security. This makes them inherently vulnerable on other network paths, such as those leading from the Internet and data centers to services in the cloud. In addition to a 360-degree view of the entire network, companies must also ensure that they are actively monitoring risk areas with the same priority.
5. Clean cloud policies regularly
The cloud security landscape is changing faster than most companies can keep up with. For this reason, cloud security groups are subject to constant change as they are constantly adjusted to take into account new applications. If companies don't update their cloud policies, they can quickly become bulky, difficult to maintain, and risky. Therefore, cloud security groups must be managed on an ongoing basis so that they are appropriate, efficient and pose no risk.
6. Implement DevSecOps
The cloud may be perfect for DevOps in terms of simple and agile provision of resources and security using infrastructure tools as code. However, this methodology is rarely used for risk analysis and recommendations for corrective action. Organizations looking to take control of their cloud security should pay attention to this. Before introducing a new risk, an automated what-if risk assessment should be obtained as part of the code pull request before acting prematurely.
From network visibility and management to risk assessment and remediation - ensuring security in a hybrid cloud environment may sound like a hassle. However, if these basic points are observed, each company can create its own security concept.
Source : https://www.it-business.de/